Digital transport systems face a 600% surge in cyberattacks between 2024 and 2025 according to recent aviation sector analysis. That single statistic captures the core challenge: as transportation infrastructure becomes more connected, it becomes exponentially more vulnerable.
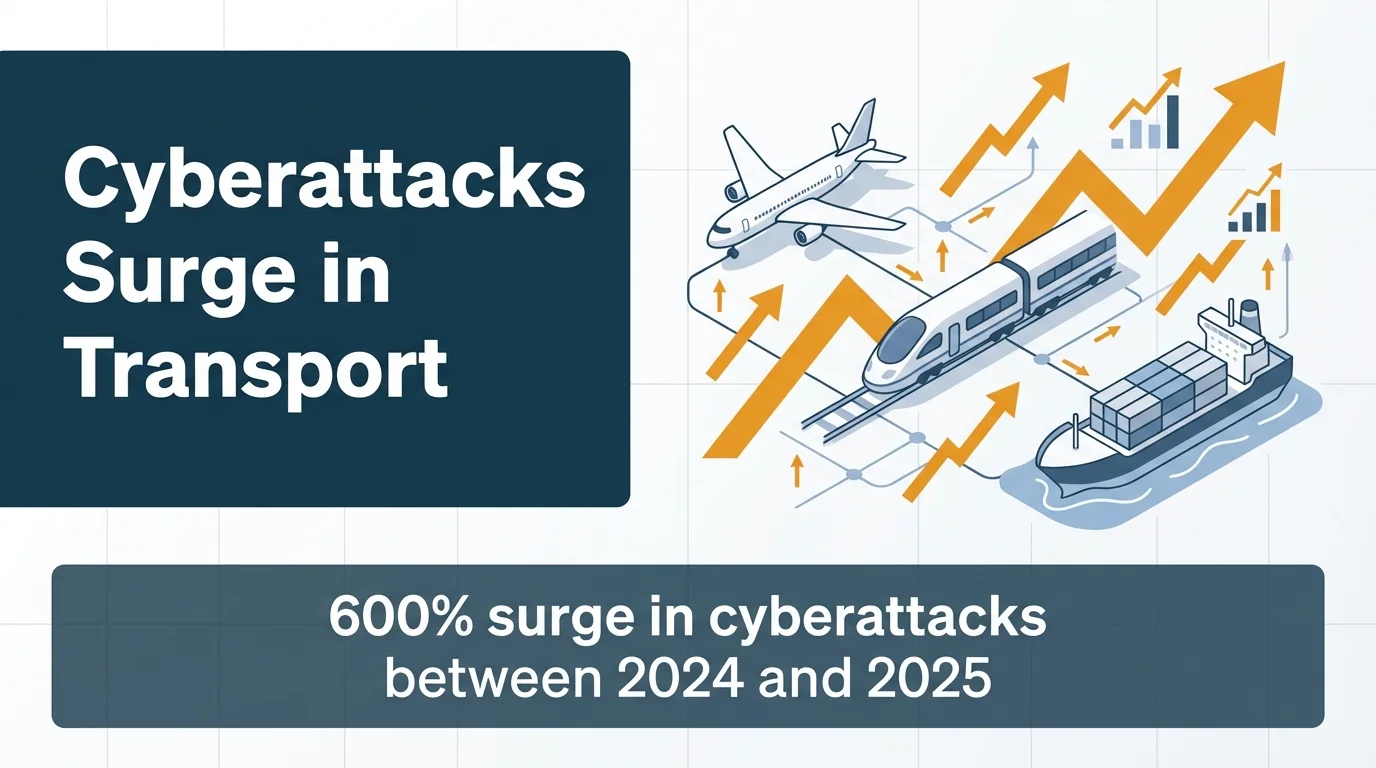
The problem extends beyond aviation. Ports, rail networks, highway management systems, and public transit all depend on interconnected digital systems.
These systems control everything from traffic signals to cargo routing. When they fail, the consequences cascade across supply chains, logistics operations, and public safety networks.
This guide examines the technical challenges facing digital transport safety. We’ll explore cybersecurity vulnerabilities, infrastructure limitations, and operational technology risks.
You’ll understand how different transport modes face distinct threats. You’ll learn why traditional IT security approaches fail in transportation contexts.
Most importantly, you’ll gain practical frameworks for addressing these challenges in your operations.
Defining Digital Transport Safety in Modern Infrastructure
Digital transport safety encompasses the security of all computerized systems managing transportation infrastructure. This includes intelligent transportation systems, operational technology networks, and connected vehicle platforms.
The scope extends far beyond traditional cybersecurity. Physical safety and digital security converge in transportation environments.
A compromised traffic management system doesn’t just risk data breaches. It threatens lives through potential collisions, delays, or infrastructure failures.
Core Components of Digital Transport Infrastructure
Intelligent transportation systems form the backbone of modern transport networks. These systems integrate sensors, cameras, communication networks, and control systems.
They manage traffic flow, coordinate public transit, and optimize logistics operations. Each component creates potential entry points for cyber threats.
Operational technology systems control physical processes. Unlike traditional IT networks that manage data, OT systems control machinery, signals, and physical infrastructure.
This distinction matters. OT systems require different security approaches than standard IT networks.
The Digital Transformation Challenge
Transportation operators face pressure to digitize operations. Digital transformation promises efficiency gains, cost reductions, and improved safety outcomes.
However, rapid digitalization often outpaces security planning. Legacy infrastructure connects to modern networks without proper security architecture.
The result creates vulnerabilities across transport modes. Aviation, maritime, rail, and highway systems all struggle with similar security gaps.
CISA identifies protecting critical infrastructure as one of its top challenges in 2026, reflecting the severity of these vulnerabilities.

Primary Cybersecurity Threats Targeting Transportation Systems
Understanding specific threats helps prioritize security investments. Transportation networks face distinct attack patterns compared to other sectors.
These attacks exploit the interconnected nature of modern transport infrastructure. They target operational technology, communication networks, and data management systems.
Ransomware Attacks on Transport Operations
Ransomware represents the most immediate threat to transportation operations. Attackers encrypt critical systems and demand payment for restoration.
Unlike data breaches, ransomware directly halts operations. A compromised rail scheduling system stops trains.
A locked port management platform prevents cargo movement. The operational impact creates urgency that attackers exploit.
Transport operators often pay ransoms to restore service quickly. This makes the sector attractive to cybercriminals seeking high-value targets.
Advanced Persistent Threats and Nation-State Actors
Sophisticated attackers target transportation infrastructure for strategic purposes. These advanced persistent threats establish long-term access to networks.
They map systems, identify vulnerabilities, and position themselves for future attacks. The goal isn’t immediate disruption but maintaining access for strategic timing.
Geopolitical tensions increase these risks. Critical transportation infrastructure becomes a target during international conflicts or trade disputes.
Phishing and Social Engineering Vulnerabilities
Human factors remain the weakest security link. Phishing attacks target transport employees with convincing fake communications.
One compromised credential can provide network access. From there, attackers move laterally through systems until reaching high-value targets.
Social engineering exploits operational pressures in transportation environments. Time-sensitive decisions, shift work patterns, and communication protocols create opportunities for manipulation.
| Threat Type | Primary Target | Impact Severity |
|---|---|---|
| Ransomware | Operational systems, scheduling platforms | Immediate service disruption |
| APT attacks | Network infrastructure, control systems | Long-term strategic compromise |
| Phishing | Employee credentials, administrative access | Gateway to broader network access |
| DDoS attacks | Communication networks, public-facing systems | Service degradation, coordination failures |
Infrastructure Vulnerabilities Across Transportation Modes
Each transportation sector faces unique security challenges. Infrastructure design, operational requirements, and legacy systems create distinct vulnerability profiles.
Understanding these differences helps tailor security approaches to specific environments.
Aviation System Vulnerabilities
Aviation relies on interconnected systems for air traffic control, flight operations, and passenger management. These systems operate in real-time with minimal tolerance for disruption.
Air traffic control networks manage aircraft separation, routing, and communication. Compromised ATC systems create immediate safety risks.
Airport infrastructure includes ticketing systems, baggage handling, security screening, and ground operations. Each system connects to broader networks, creating multiple attack surfaces.
The complexity of airline partnerships amplifies these vulnerabilities. Code-sharing agreements, alliance memberships, and third-party service providers extend network boundaries beyond single organizations.
Maritime and Port Security Challenges
Ports function as critical nodes in global supply chains. They coordinate vessel traffic, cargo handling, customs processing, and intermodal transfers.
Port management systems control cranes, automated guided vehicles, and gate operations. These operational technology systems integrate with business systems for documentation and billing.
Maritime communication relies on satellite networks and radio systems. These channels face interception risks and spoofing attacks.
GPS manipulation represents a specific threat to maritime operations. Attackers can spoof location data, misdirecting vessels or disrupting automated navigation.
Rail Network Operational Technology Risks
Rail systems depend on signaling networks that control train movements. These systems prevent collisions through automated block control and interlocking mechanisms.
Legacy signaling infrastructure often dates back decades. Modernization efforts connect old systems to new digital networks without comprehensive security architecture.
Passenger rail adds complexity through ticketing systems, passenger information displays, and station management platforms. Freight rail integrates with logistics networks and customer systems.
The geographic distribution of rail infrastructure creates monitoring challenges. Signals, switches, and communication equipment span hundreds of miles, complicating physical security.
Highway and Traffic Management System Exposure
Intelligent transportation systems manage highway operations through sensors, cameras, and dynamic signage. These systems optimize traffic flow and coordinate incident response.
Traffic signal networks control intersections across entire metropolitan areas. Centralized management creates efficiency but concentrates risk in control systems.
Connected vehicle infrastructure introduces vehicle-to-infrastructure communication. This enables safety features but creates new attack vectors through wireless communication protocols.
Highway management systems integrate with emergency services, transit operations, and private navigation services. These integrations expand the potential impact of security breaches.
Operational Technology Security Versus IT Security
Transportation operators must understand the fundamental differences between operational technology and information technology security. These distinctions shape effective security strategies.
Standard IT security practices often fail when applied to OT environments. The different priorities, constraints, and architectures require specialized approaches.
Availability Requirements in OT Environments
Operational technology prioritizes availability above all else. Systems must run continuously without interruption.
IT systems can tolerate scheduled maintenance windows. OT systems controlling trains, traffic signals, or flight operations cannot stop for security updates.
This constraint complicates patch management. Security updates require extensive testing to ensure they don’t disrupt operations.
The result often means delayed patching, leaving known vulnerabilities unaddressed longer than IT best practices recommend.
Network Segmentation and Air Gaps
Effective OT security requires strict network segmentation. Operational systems should remain isolated from business networks and internet connections.
However, digital transformation pushes toward integration. Remote monitoring, predictive maintenance, and data analytics all require connectivity.
This creates tension between operational efficiency and security. Each connection point represents a potential vulnerability.
Proper segmentation uses industrial firewalls, unidirectional gateways, and demilitarized zones to control traffic between network segments.
Legacy System Integration Challenges
Transportation infrastructure includes equipment operating for decades. These legacy systems were never designed with cybersecurity considerations.
They lack authentication mechanisms, encryption capabilities, or security logging. Yet they control critical functions that cannot be easily replaced.
Securing legacy systems requires compensating controls. Network-level security, monitoring systems, and access restrictions protect vulnerable equipment.
Replacement strategies must balance security improvements against operational disruption and capital costs.
| Security Aspect | IT Approach | OT Requirements |
|---|---|---|
| Priority order | Confidentiality, integrity, availability | Availability, integrity, confidentiality |
| Patching cadence | Monthly or automated updates | Extensively tested, scheduled during maintenance windows |
| Network architecture | Connected for collaboration and access | Segmented with controlled connections |
| System lifespan | 3-5 years typical replacement cycle | 15-30 years operational lifetime |
Emerging Technologies and Security Implications
New technologies promise operational improvements but introduce novel security challenges. Transportation operators must evaluate both benefits and risks.
Understanding these implications helps make informed technology adoption decisions.
Connected and Autonomous Vehicle Security
Autonomous vehicles rely on sensors, processors, and communication systems working together. Each component creates potential attack surfaces.
Vehicle-to-vehicle communication enables collision avoidance and traffic coordination. However, these wireless channels face interception and manipulation risks.
Vehicle-to-infrastructure communication connects vehicles to traffic management systems. Compromised infrastructure could send malicious commands to vehicles.
The software complexity in autonomous systems creates vulnerability opportunities. Millions of lines of code inevitably contain exploitable bugs.
IoT Sensors and Smart Infrastructure
IoT devices proliferate across transportation infrastructure. Sensors monitor traffic, track assets, measure environmental conditions, and report system status.
Many IoT devices lack robust security features. Default passwords, unencrypted communication, and missing update mechanisms create vulnerabilities.
The sheer quantity of devices complicates security management. Thousands of sensors across a transportation network require monitoring and maintenance.
Compromised IoT devices serve as entry points to broader networks. Attackers exploit weak sensors to gain initial access before moving to high-value targets.
Cloud Computing and Data Processing
Cloud platforms offer scalability and analytical capabilities for transportation data. Traffic management, predictive maintenance, and operational analytics benefit from cloud computing.
However, cloud adoption requires careful security architecture. Data transmission between operational systems and cloud platforms must be protected.
Third-party cloud providers introduce supply chain risks. Transportation operators must evaluate provider security practices and contractual protections.
Data residency and sovereignty concerns complicate international operations. Critical infrastructure data may face regulatory restrictions on cloud storage locations.
Artificial Intelligence and Machine Learning Applications
AI systems optimize routing, predict maintenance needs, and detect anomalies in transportation operations. These capabilities improve efficiency and safety.
Yet AI systems face adversarial attacks. Carefully crafted inputs can manipulate AI decision-making, causing misclassifications or incorrect predictions.
Training data poisoning represents another threat. Attackers who compromise training datasets can embed vulnerabilities into AI models.
The opacity of AI decision-making complicates security validation. Understanding why an AI system made a particular decision can be difficult, hindering threat detection.
Regulatory Frameworks and Compliance Requirements
Transportation operators navigate complex regulatory environments. Security requirements come from multiple jurisdictions and governing bodies.
Understanding these frameworks helps ensure compliance while building effective security programs.
Critical Infrastructure Protection Standards
Governments designate transportation systems as critical infrastructure requiring special protection. This designation brings security requirements and oversight.
Standards vary by jurisdiction but generally mandate risk assessments, security controls, and incident reporting. Operators must document security measures and demonstrate compliance.
The challenge lies in harmonizing different standards. International operations face multiple regulatory regimes with potentially conflicting requirements.
Industry-Specific Security Requirements
Each transportation mode has sector-specific regulations. Aviation follows standards from aviation authorities.
Maritime operations comply with international maritime security codes. Rail and highway systems face national transportation security requirements.
These sector standards often address physical security more than cybersecurity. Operators must interpret how traditional security requirements apply to digital systems.
Data Protection and Privacy Regulations
Transportation systems collect extensive data about passenger movements, cargo shipments, and operational performance. This data faces privacy regulations.
Passenger data requires protection under privacy laws. Location tracking, payment information, and travel patterns all qualify as personal data.
Data retention policies must balance operational needs against privacy requirements. Keeping data longer than necessary increases both regulatory risk and potential breach impact.
Cross-border data transfers face additional restrictions. International transportation operations must address data sovereignty requirements.
Best Practices for Transportation Security Implementation
Effective security requires comprehensive approaches tailored to transportation environments. These best practices address the unique challenges operators face.
Implementation should prioritize based on risk assessment and operational requirements.
Risk Assessment and Threat Modeling
Start with thorough risk assessments identifying critical assets and potential threats. Map all systems, connections, and dependencies across your transportation infrastructure.
Threat modeling helps prioritize security investments. Consider both likelihood and potential impact when evaluating threats.
Include physical and cyber threats in your assessment. Transportation infrastructure faces both, often simultaneously.
Update assessments regularly as systems change and new threats emerge. Annual reviews minimum, with interim updates after significant changes.
Defense in Depth Architecture
Implement multiple security layers rather than relying on single controls. Network segmentation, access controls, monitoring systems, and incident response capabilities work together.

Each layer compensates for potential failures in others. Attackers must overcome multiple barriers to reach critical systems.
Perimeter security alone fails in modern threat environments. Internal segmentation limits lateral movement after initial compromise.
Monitor traffic between segments to detect unusual patterns. Baseline normal operations to identify anomalies quickly.
Access Control and Identity Management
Restrict system access based on role requirements. Operators need different permissions than administrators or maintenance personnel.
Implement strong authentication for all system access. Multi-factor authentication should protect administrative functions and sensitive systems.
Review and audit access privileges regularly. Remove access promptly when personnel change roles or leave the organization.
Monitor privileged account usage to detect unauthorized access or insider threats. Log all administrative actions for security review.
Continuous Monitoring and Threat Detection
Deploy monitoring systems across network segments and critical infrastructure. Collect logs from operational technology systems, network devices, and security controls.
Security information and event management platforms aggregate data for analysis. Automated correlation helps identify attack patterns across multiple systems.
Establish baseline behavior for systems and networks. Anomaly detection identifies deviations that may indicate security incidents.
Response procedures should address the operational constraints of transportation systems. Incident response must balance security needs with operational continuity.
Encryption and Data Protection
Encrypt data in transit between systems and facilities. Virtual private networks protect remote connections and inter-site communications.
Encryption requirements must consider operational technology constraints. Some legacy systems cannot support modern encryption protocols.
In these cases, encrypt at network boundaries using security gateways or protocol converters. Protect the communication channel even if endpoints lack native encryption.
Data at rest also requires protection, particularly for passenger information, operational data, and security logs.
Vendor and Supply Chain Security
Assess security practices of technology vendors and service providers. Third-party access to your systems extends your attack surface.
Contractual requirements should mandate security standards for vendors. Include provisions for security audits and incident notification.
Software supply chain security matters for transportation systems. Verify the integrity of updates and patches before deployment.
Hardware supply chain risks require attention for critical infrastructure. Source equipment from trusted suppliers with verified provenance.
Future Trends in Digital Transport Security
Transportation security continues to develop as technology and threats advance. Understanding these trends helps prepare for future challenges.
Strategic planning should account for these developments over the next five years.
Quantum Computing Implications
Quantum computers will eventually break current encryption standards. Transportation operators must plan for post-quantum cryptography migration.
The timeline remains uncertain, but preparation should begin now. Inventory systems using encryption and assess upgrade paths.
Critical infrastructure with long operational lifespans faces particular challenges. Systems deployed today may still operate when quantum computers mature.
Zero Trust Architecture Adoption
Zero trust principles assume breach and verify every access request. This approach suits transportation environments with diverse users and systems.
Implementation requires identity-centric security rather than network-perimeter defenses. Every user, device, and system requires authentication and authorization.
Micro-segmentation limits lateral movement within networks. Compromised systems cannot easily access other network segments.
Zero trust aligns with operational technology security needs by enforcing strict access controls and continuous verification.
Artificial Intelligence for Security Operations
AI-powered security tools will become essential for managing complex transportation networks. Machine learning improves threat detection and reduces false positives.
Automated response capabilities can contain threats faster than manual processes. This matters in time-sensitive transportation operations.
However, AI security tools require careful implementation. Training, tuning, and validation ensure they enhance rather than hinder security operations.
Increased Regulatory Requirements
Expect expanding cybersecurity regulations for critical infrastructure. Governments recognize the strategic importance of transportation security.
Requirements will likely mandate specific security controls, reporting obligations, and incident disclosure. Operators should participate in regulatory development to ensure practical requirements.
International harmonization efforts may create consistent standards across jurisdictions. This would simplify compliance for global transportation operators.
Collaborative Security Initiatives
Information sharing between transportation operators improves collective security. Threat intelligence helps organizations prepare for emerging attacks.
Industry-specific information sharing and analysis centers facilitate collaboration. These forums share indicators of compromise and attack patterns.
Public-private partnerships between government agencies and operators enhance critical infrastructure protection. Shared situational awareness benefits all participants.
Building these relationships takes time. Start participating in relevant forums and establishing trusted contacts now.
Building Resilience in Transportation Operations
Security alone cannot prevent all incidents. Resilience ensures transportation systems can withstand and recover from attacks.
This requires planning, preparation, and tested response capabilities. Resilient operations maintain essential functions even during security incidents.
Backup systems and redundancy prevent single points of failure. Critical functions should have alternative operational modes if primary systems fail.
Incident response plans specific to transportation environments account for safety requirements and operational constraints. Test these plans regularly through tabletop exercises and simulations.
Recovery capabilities determine how quickly operations resume after incidents. Maintain tested restoration procedures for critical systems.
Staff training ensures personnel can execute security and response procedures effectively. Regular exercises build muscle memory for crisis situations.
The complexity of digital transport safety challenges requires sustained attention. No single solution addresses all vulnerabilities.
Start with risk assessment to identify your highest priorities. Implement security controls systematically based on operational requirements.
Balance security investments with operational needs. Perfect security isn’t achievable, but meaningful improvements reduce risk substantially.